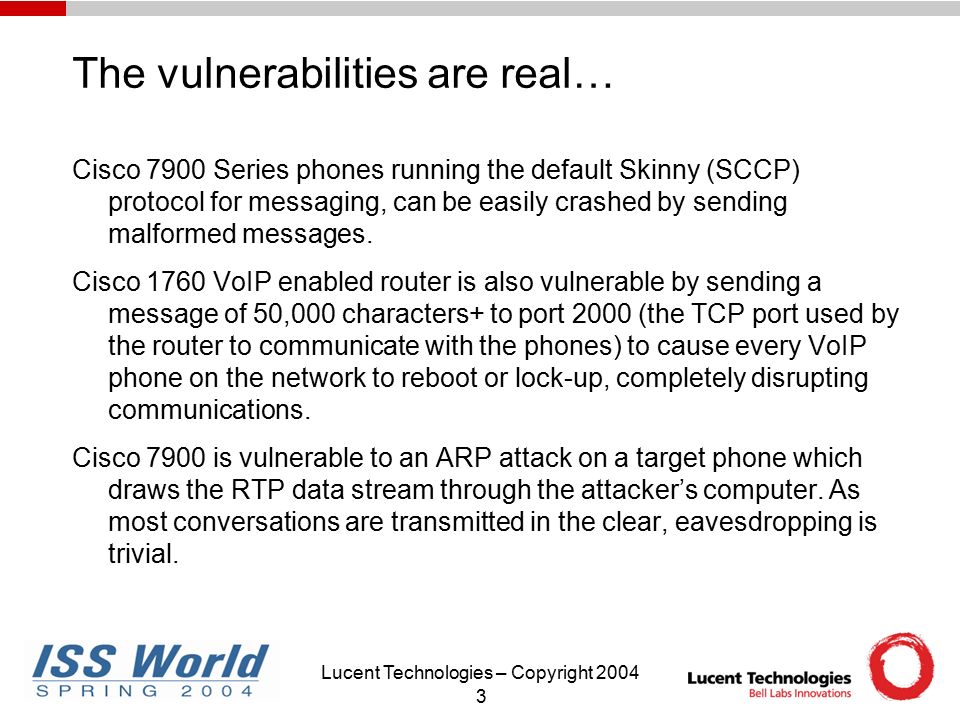
Track A: Network Security 9AM-10AM May 6, 2004 Security And Next Generation VoIP George G. McBride Senior Manager, Security Practice Lucent Technologies. - ppt download

Interview #common #questions TCP/UDP port numbers. For cyber security professionals you can also think about the payloads you can use if these ports are open. #indincybersecuritysolutions #cybersecurity... - Indian Cyber Security Solutions -




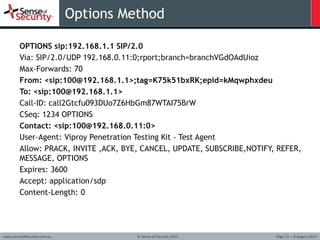
![How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub](https://packt-type-cloud.s3.amazonaws.com/uploads/sites/2432/2018/06/b534d740-13bf-4799-8835-d7940f267db5.png)




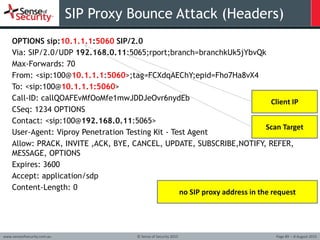
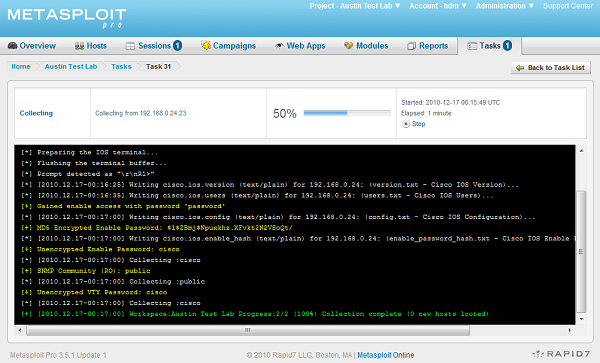
![How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub](https://packt-type-cloud.s3.amazonaws.com/uploads/sites/2432/2018/06/d2578ffa-594d-4f53-acf3-49746685408f.png)


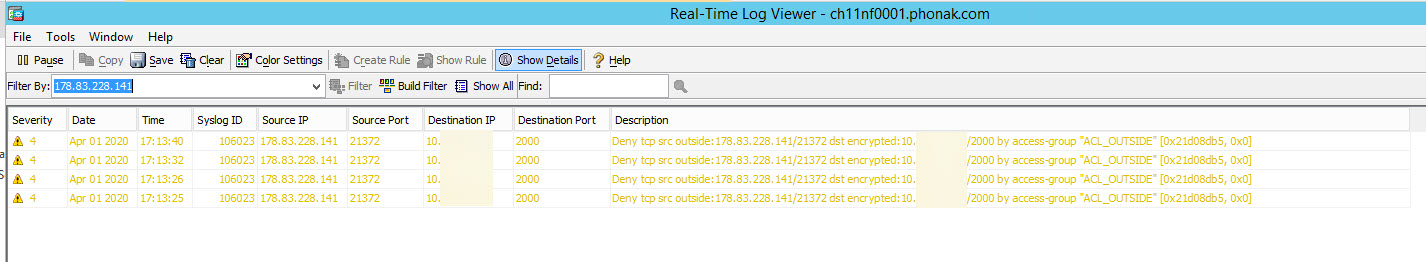
![How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub How to attack an infrastructure using VoIP exploitation [Tutorial] | Packt Hub](https://packt-type-cloud.s3.amazonaws.com/uploads/sites/2432/2018/06/8e94a4b8-5b79-40a9-be92-abe3ad36cc29.png)